Huntress has been authorized by the Common Vulnerabilities and Exposures (CVE) Program as a CVE Numbering Authority (CNA). This sounds fancy (and it is), but you’re probably wondering, “What does all this mean?” Well, I’m glad you asked.
What Is the CVE Program?
The CVE Program’s mission is to “identify, define, and catalog publicly disclosed cybersecurity vulnerabilities.” This program is an international, community-driven effort that relies on established cybersecurity experts to find vulnerabilities. It’s essentially the all-knowing directory for spotting and naming security threats. By centralizing the knowledge of vulnerabilities, defenders can focus on managing their vulnerability management programs rather than trying to check multiple sources for what needs attention.
Why Is the CVE Program Important?
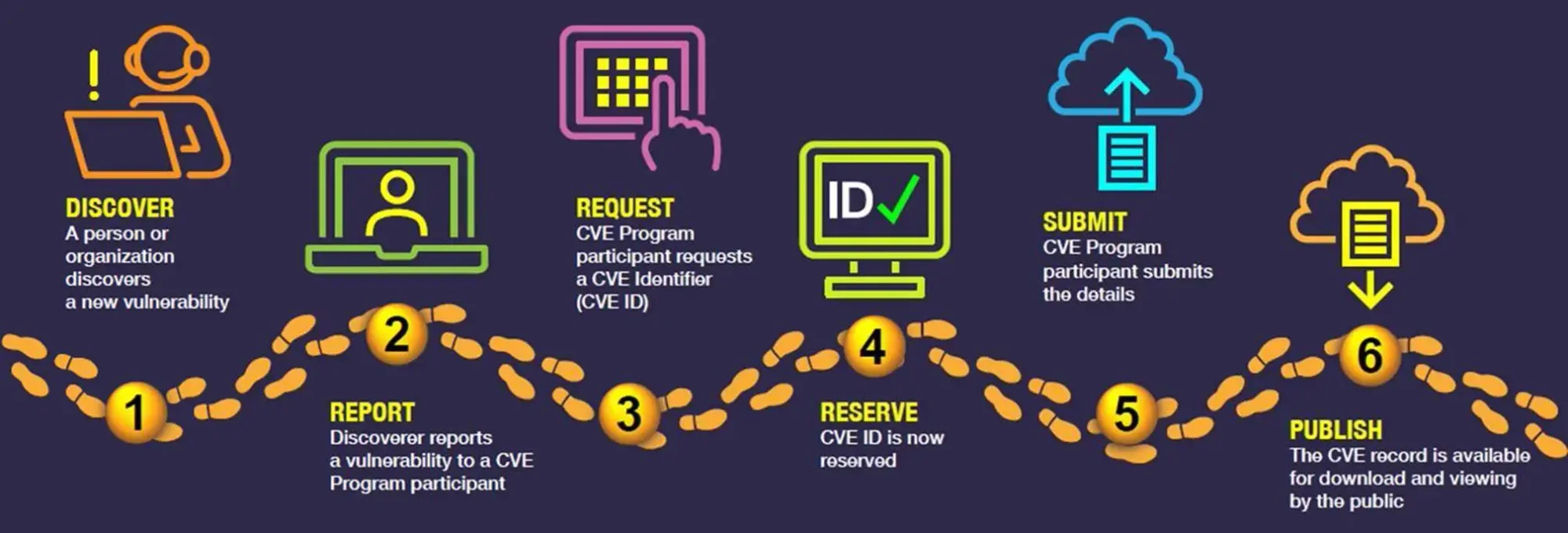
The CVE Program establishes a single source of truth for cybersecurity threats. When a cybersecurity expert discovers a vulnerability, it gets assigned a CVE ID and is published to the CVE List. This means everyone's on the same page when IT and cybersecurity professionals talk about a specific vulnerability. There’s no confusion about which threat they’re talking about.
The CVE Program allows people and tools worldwide to refer to the same vulnerability, which is critical when time is of the essence. That means individuals and organizations don’t have to piece together various descriptions of the same issue——through clear, consistent descriptions and names, we all know exactly what we’re dealing with, which streamlines response and mitigation efforts. These CVEs are also used when scanning environments for the presence of vulnerabilities. Those scanners are hunting for the presence of vulnerable software as reported by CVEs.
Why Is CVE Numbering Authorization Relevant to Huntress?
Our participation in the CVE Program means we’re contributing to a global database that helps everyone, not just our clients. The CVE List feeds into the U.S. National Vulnerability Database (NVD), enabling rapid discovery and correlation of vulnerability information. This means better protection for systems worldwide against cyberattacks.
Huntress has been critical in providing community education, outreach, and defense when emergent threats and vulnerabilities arise that need immediate action by the community. By registering as a CNA, we’ll have the ability to author CVEs when necessary. As a requirement for CISA outreach, this allows for faster dissemination of threat information.
Like Huntress, the CVE Program Is Grounded in Community
The CVE Program relies on experts throughout the globe to discover and report vulnerabilities, meaning there’s tremendous collaboration among the best minds in cybersecurity. We’re all working together, constantly updating and refining the CVE List, making it a reliable go-to resource for everyone involved.
Huntress has always watched over the 99% of small- to medium-sized enterprises that comprise our economy's backbone, providing community education and protection when vulnerabilities are being exploited against them. As a CNA, we’ll proudly stand alongside other trusted organizations to ensure vulnerabilities are identified, exposed, and made known.
With just 382 CNA organizations worldwide, Huntress joins an exclusive group of roughly 200 CNAs in the U.S. Together, we’ll work diligently to communicate consistent descriptions of vulnerabilities that IT and cybersecurity professionals can use to discuss, prioritize, and address the threats that leave businesses and infrastructure at risk for cyberattacks.
If you’d like to dive deeper into the critical importance of patching known CVEs in your environment, download our 2024 Cyber Threat Report.