Capture The Flag: Test Your Skills
Think you can outsmart a hacker? Prove it. Our interactive Capture The Flag challenge lets you step into the attacker’s shoes, so you can beat them at their own game.
Cybersecurity Awareness: Defense Done Differently
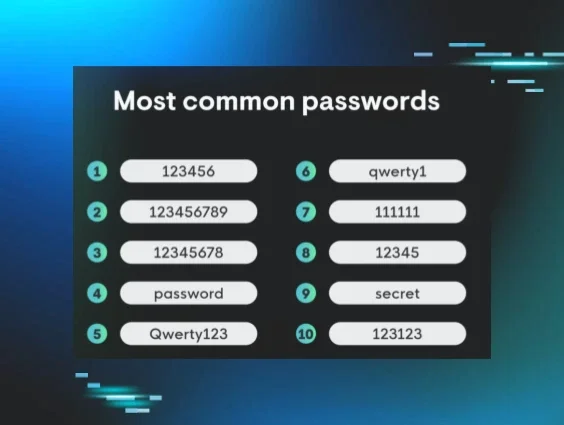
Cybersecurity awareness isn’t about scaring people into strong passwords or another set of “dos and don’ts” you’ll forget tomorrow. It’s about giving you the tools and knowledge to stop attackers in their tracks—before they have the chance to make headlines.
Here, you’ll find hands-on resources, events, and challenges to help uplevel your skills, and practical tips to make security second nature, whether you’re brand new to cybersecurity or looking to sharpen your defenses.


Join us for Tradecraft Tuesday, a monthly session covering threat actor tactics on the rise, recent, real-life security incidents, and methods you can use to defend against threats.
October gets busy. Webinars, live workshops, in-person meetups—you name it. Check out our event calendar, mark your favorites, and learn how to take the fight to the attackers