Learn more in a comprehensive walkthrough




With the majority of incidents now tied to identity threats, you need a purpose-built solution for continuous threat protection against critical risks like account takeovers and business email compromise (BEC).

Attackers grab session tokens—the digital keys that keep users logged in—and import them into their own browsers. No password is needed, just instant access. Our ITDR stops hackers from exploiting your systems and bypassing your 2FA/MFA.

Identity is the new attack surface, and usernames and passwords are the new way into your business. Huntress Managed ITDR keeps cybercriminals out by closing blind spots across your workflows and locking down your identities.
Malicious OAuth apps are a go-to move for attackers to steal data and maintain persistence. Get a full view into every rogue app installed across tenants and proactively find Traitorware and Stealthware before they do damage.

Detect and respond to anomalies that go bad fast. Huntress Managed ITDR exposes unusual login locations and VPNs so only authorized users can access your data.

Business email compromise (BEC) isn’t just about tricking users—it’s about taking over your inbox. Huntress’ ITDR solution spots unusual activity and protects your inbox.

Only Huntress gives you visibility, validation, and remediation. We don’t just alert–we respond, with SOC-backed action and clear guidance for remediation.

Unlike others, we don’t just forward logs and waste your time. Every alert we send is packed with context: human-validated, primed for action, and purpose-built to wreck the identity tradecraft hackers love to abuse.
Clock out with confidence knowing our expert team never takes our eyes off your identities. Our AI-assisted threat hunters watch your Microsoft 365 and Google Workspace environments to stop threats 24/7.
Enterprise-grade protection shouldn’t come at a hefty price. We’ve designed our ITDR to wreck hackers, not budgets. It works with all levels of Microsoft and Google licensing for full protection within minutes of deployment.
When BEC happens, you need to know: How they got in. What they took. When they got kicked out. Timeline provides the answers without hours of log review.
The Incident Report Timeline doesn’t just tell you what happened—it shows you how it all went down. From the first suspicious blip to full-blown incident, you get a clear, chronological view of attacker activity and exactly what Huntress did to shut it down. Every move. Every response. No guesswork.
Start to finish, it lays out the entire story—so you can understand the true scope, see the impact, and walk away confident the threat is dead and buried.



Learn more in a comprehensive walkthrough
Learn more about the types of Rogue Apps you need to watch out for
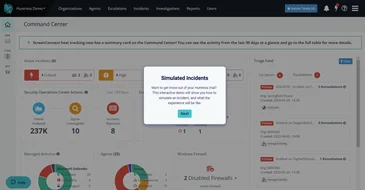
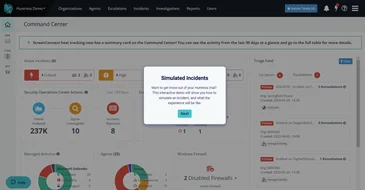
Get hands-on with a simulated ITDR incident


See how Huntress ITDR and Trumbull Tech help an accounting company avoid financial ruin.

Managed Identity Threat Detection & Response (ITDR) is a fully managed security solution provided by Huntress. It continuously monitors and protects your identities and email environments within Microsoft 365 against identity-focused cyber threats like unwanted logins, session hijacking, credential theft, and malicious inbox rules. Acting as the first line of defense, it ensures that only authorized users can access your system.
Huntress Managed ITDR addresses major security challenges such as session hijacking, credential theft, malicious inbox and forwarding rules, and account takeover or business email compromise (BEC) attempts. It solves the problem of detecting and responding to identity-based threats within Microsoft 365 preventing unauthorized access and potential damage to your business operations.
Huntress Managed ITDR gives you 24/7 identity monitoring and response from experienced threat analysts who detect and respond to threats in real time. This service can cover platforms like Microsoft 365 and minimizes noise by only alerting you to truly malicious activities. It also offers automated remediation when necessary. This level of comprehensive protection lets you safeguard your identities effectively without the need for an in-house security team.
Huntress Managed ITDR protects both Microsoft 365 and Google Workspace (GWS) ecosystems, so users can easily standardize on one identity defense platform across Microsoft and Google.
Yes, ITDR released its Incident Report Timeline in January 2026. The Timeline offers a detailed, chronological view of the events surrounding an Incident Report. This includes the suspicious activities that triggered the report, as well as the specific actions Huntress took to remediate the threat. By reviewing the timeline, you can see the full sequence of the incident—from the initial compromise to the final resolution—helping you confirm the scope of the attack and verify that the threat has been neutralized.




What businesses and MSPs alike are saying about Huntress ITDR.