Identify and remediate malicious files, privilege escalations, viruses, lateral movement, and other suspicious hacker activity with Huntress Managed Endpoint Detection and Response (EDR) powered 24/7 by our security researchers.





Learn how malicious process detection works with Huntress.

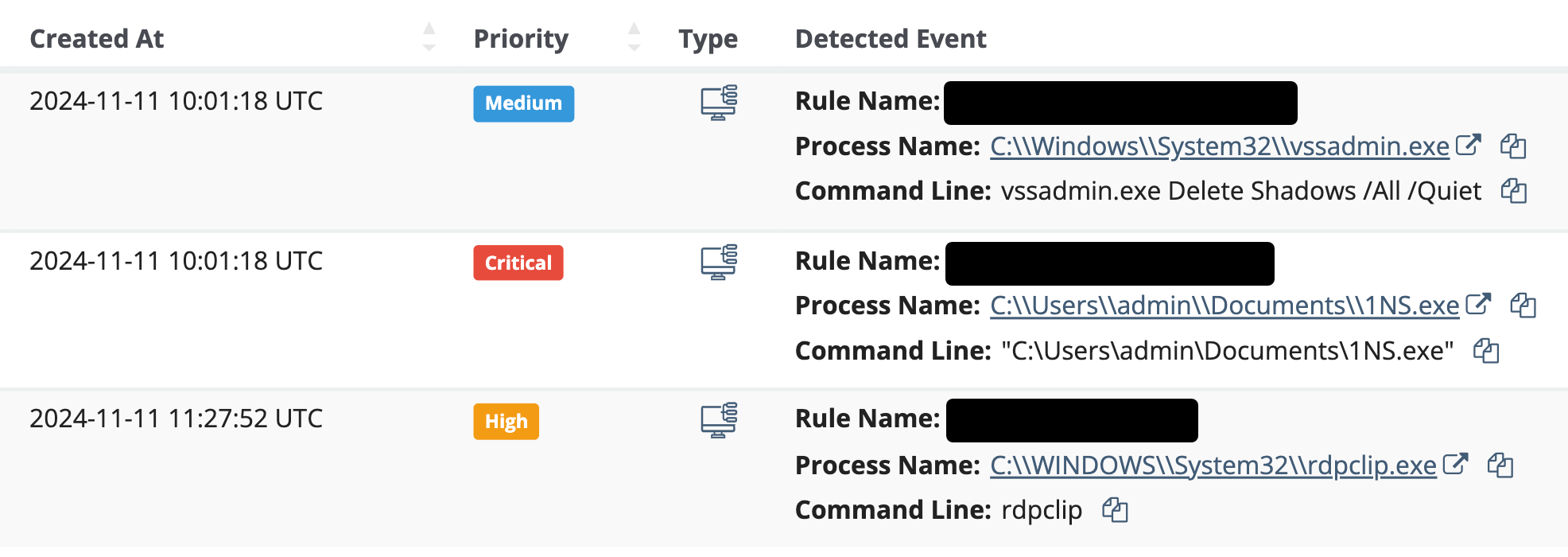
Using system process data, we can see malicious elements that try to obfuscate their attacks through legitimate software.

When our detectors spot something suspicious, we collect additional logs and process data related to the activity to create a full tree of information, giving us a deeper understanding of what is happening.

The Huntress SOC knows how to think like a hacker. They work 24/7 to detect and investigate potential threats, remediate incidents, and assist with any issues.
Remediate issues automatically or in a single click. You’ll have guidance written in a plain, jargon-free way to quickly get your systems back into a healthy state.

New tools to infiltrate environments and exfiltrate sensitive data and money are released every day. But, while the tools often change, attacks are usually built on the same techniques that have been around for years.
Attackers leverage many techniques to achieve their goals, like making their targets slip up and run a malicious process on their behalf, hiding malware in a document, or exploiting a vulnerability through another piece of software. Thankfully, when hackers weaponize legitimate software, they leave traces in the system we can follow.
The malicious process behavior feature included in Huntress Managed EDR analyzes all processes running on a system and looks for suspicious activity. This could consist of processes that are spawning from illegitimate programs or, in a lot of cases, legitimate programs used in the wrong way. Our SOC analysts will investigate suspicious behavior, create custom incident reports, and provide one-click approval for remediation.

Through continual monitoring and deep visibility into the processes running in an environment, you can take back control of your endpoints and prevent attackers from doing any damage.