



There’s a reason ransomware is such a popular form of malware in the modern hacker’s tool belt: it’s effective. The sooner you can detect ransomware, the sooner you can assess the scope of an attack and activate your incident response plan.
Like the old canary in the coal mine, our Ransomware Canaries enable faster detection of potential ransomware incidents.
When deployed, small lightweight files are placed on all protected endpoints. If those files are modified or changed in any way, an investigation is opened with our Security team to confirm whether those changes are the result of a ransomware infection or malicious encryption.
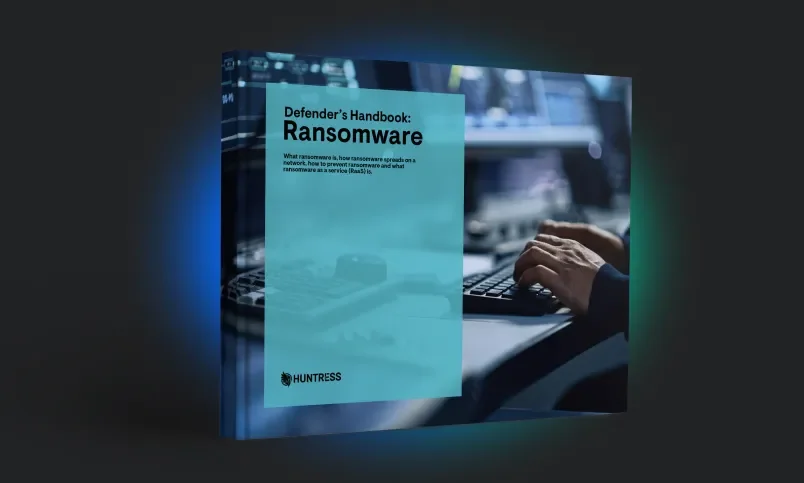
Get an end-to-end overview of ransomware - including how it spreads, key terms and definitions, and more. This Defender's Handbook answers key questions such as:


With faster alerting of potential ransomware, you can respond swiftly to remove malware and keep an infection from spreading.

By understanding exactly which endpoints have been affected by a ransomware incident, you can better assess the scope of an attack and respond as appropriate.

If a canary is tripped, our SOC team opens an investigation to verify the threat (and remove false positives)—and will work with you to ensure proper remediation occurs.
Huntress canaries are small, benign files that take up very little space and cause no disruption for end users.


Once deployed, your Huntress dashboard provides regular status updates to show the number of “armed” and “tripped” canaries—which can be viewed in aggregate or for specific endpoints. With easy access to more detailed reports, insights and remediation actions, your team can confidently respond to potential ransomware attacks—and get rid of ransomware faster.


