Cybercrime isn’t just a threat. It’s more of a guarantee.
It’s estimated that by 2025, cybercrime will cost the world an unbelievable $10.5 trillion annually. Should this prediction come true, cybercrime will have secured its spot as the third-largest economy in the world after the United States and China.
The risk of a cyberattack mimics the risk of a natural disaster. Residents who live along the coastline know they may experience hurricanes during certain months of the year. Folks who occupy the midwest are aware that they may see a tornado or two roll through. Northeast residents have their snow shovels on standby during the winter months.
The commonality between occupants of these regions? They plan accordingly.
They know what the risks are, and they prepare: Floridians prepare for hurricanes; Kansans prepare for tornadoes; Bay Staters prepare for winter storms. These folks know that it’s not a matter of if a major weather event will strike; it’s a matter of when.
What’s interesting is that the cost of the nearly 300 natural disasters that targeted the United States between 1980 and 2020 totals $1.875 trillion—notably less than the predicted global $6 trillion cost of cybercrime damages for this year.
We're prepared for natural disasters. Why aren’t we more prepared for cyberattacks?
Separating Fact From Fiction
One reason for the lack of preparedness is that there’s a lot of incorrect or outdated information out there. This can lead to the perception that businesses are safer than they actually are.
Let’s break down a few myths surrounding cybersecurity.
- The myth: “I have Product ABC, which claims total protection against today’s threats. My business is safe.”
- The reality: Unfortunately, it’s not that simple.
Lots of endpoint protection providers claim that they’re all-encompassing solutions. However, there’s no one solution that does it all. Hackers get smarter and circumvent a new preventive tool every day. It’s only a matter of time before they get past the “latest and greatest” tools that exist today.
- The myth: “My business isn’t popular enough to have cybercriminals targeting it.”
- The reality: Cybercriminals gravitate toward easy paths to victory.
They know that the small mom-and-pop shop probably lacks the money and resources to invest in cybersecurity. As a result, smaller businesses make the perfect targets for cybercriminals. Hackers know they can make their money without expending a ton of effort.
The gap is closing between small- to medium-sized businesses (SMBs) and larger companies that fall victim to a cyberattack. In 2020, SMBs experienced less than half the number of breaches that large organizations fell victim to. In 2021, the difference is far less pronounced: SMBs experienced nearly 86% of the number of breaches that large organizations experienced.
No business is immune to cyberattacks, no matter if it’s a well-known organization or if it just opened its doors yesterday.
- The myth: “It’ll be less expensive to deal with a breach than to add a ton of layers and tools to my stack.”
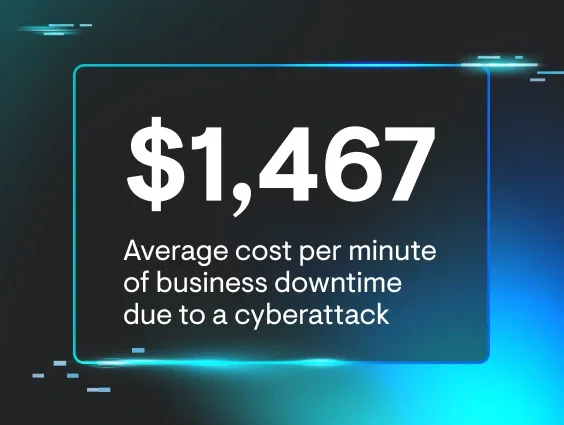
- The reality: Breaches are far more expensive than many of us give them credit for.
First, there’s the actual cost of the breach. These costs can range from thousands to millions of dollars. According to IBM Security, the average cost of a data breach in 2021 was $4.24M—a nearly 10% increase since 2020.
Why so high? There are several categories of costs to consider:
1. Detection and escalation. This includes paying staff members to carry out various duties, such as investigating the breach, assessing the damage, notifying stakeholders and executing an incident response plan.
2. Loss of business. Having to shut down normal operations until the incident is mitigated can be costly. Further, the business may lose customers and prospects as a result of reputational damage.
3. Notification to third parties. Businesses must tell their customers when a breach that may have exposed their personal information has occurred, whether they send emails and letters or make phone calls. This category also includes the cost to recruit the help of outside experts to mitigate the situation.
4. Post-breach response. This cost category focuses on helping the victims of the breach, including ensuring staff is available to provide customers with comprehensive support, issuing credit monitoring or other similar services, product discounts and other items to compensate customers following the breach.
Then, there’s the cost of intangibles—for example, the loss of credibility and reputation. It can take many years and funds to build back the trust of customers and prospects—if it’s even possible at all.
Check out our Cost of Downtime calculator to self-assess your current level of exposure and the financial impact an incident might have on your business.
It’s better—and far more cost-effective—to layer up your security stack to stop attackers in their tracks than to do damage control after an incident occurs.
The Right Security Stack
There’s no doubt about it: the best security stack features a combination of humans and tools.
The right security tools can help prevent some attacks from happening or assist with slowing down the progress of any active incidents.
However, it bears repeating: no one tool can do it all.
It’s better to layer up and proactively approach prevention and remediation. Taking those measures now can save you thousands or even millions of dollars in the long run, depending on the size of your company.
It’s also good to remember to regularly evaluate your security stack to make sure it evolves as your business grows. What compiled the best security stack yesterday may leave the door wide open for hackers today. Bad actors never stop leveling up their knowledge on hacking into environments. You should never stop leveling up your efforts to make it as hard as possible for them to do so.
The human element is critical, too. There’s simply no replacement for the expertise and contextual awareness that human threat hunters bring to the table. There are several ways to approach introducing humans to your security stack.
1. Hire full-time staff members.
Full-time staff members who have cybersecurity expertise can be great additions to a team—but this approach can get expensive fast.
According to data from the value-added reseller (VAR) and managed service provider (MSP) talent recruiting specialists at VAR Staffing, the average salary of the candidate pool for a ThreatOps Security Analyst was $125,833. It’s important to note that the candidates in this pool fell in the “mid-level” range of experience, and salary ranges could likely skew higher depending on the specific needs and requests of the hiring organization. Further, ThreatOps Security Analysts tend to find a new opportunity every 18 to 24 months, which places a recruitment burden on the companies that hire them.
Because of these factors, many companies find that it’s easier to employ a solution instead.
2. Employ a solution that includes a human component.
Employing a solution releases the staffing and salary burdens from companies and is often a much cheaper—yet still viable—addition to a security stack. The vendor absorbs those burdens and costs while still lending out the expertise of their human threat hunters to observe and flag suspicious activity. It’s like working with an agency to deploy human security guards in your virtual environments to keep attackers at bay.
Strengthen Your Defense With a Good Offense
While there is no one solution that does it all, a layered approach that includes human threat hunters and security tools can help you make it harder for hackers to break in. Plus, the investment in the proper security stack can ultimately save your business much more than just money.
With the rising costs associated with cybersecurity incidents, it’s best to strengthen your defense to stay one step ahead of savvy threat actors.
Ready to deploy Huntress’ human threat hunters to defend your environments? Sign up for a free trial.