Endpoint detection and response (EDR) has changed the game.
With attack surfaces growing and the need to keep remote and hybrid environments safe, EDR has become one of the most powerful tools in an organization's cybersecurity arsenal. EDR brings exceptional visibility into our most vulnerable area: endpoints. On top of that, it provides the power to monitor and respond more quickly to today’s threats.
But an EDR solution alone does not give your organization EDR capabilities.
Without the right team and time commitment to manage EDR solutions, they can amass large amounts of data and alerts, leading to higher costs and overburdening analysts. That’s why many businesses are asking themselves, “should I consider a managed EDR solution?”
In this blog, let’s walk through what EDR is, the differences between managed EDR and unmanaged EDR, and how to choose the best fit for your business.
What is EDR?
EDR is an endpoint security solution that monitors, detects, and responds to cyber threats in real time. EDR creates unparalleled visibility and detection across endpoints and enables organizations to address attacks swiftly.
There are five key components of EDR:
1. Data collection and analytics
2. Detection
3. Visibility
4. Response
5. Reporting and alerts
These five functions all work together to give users clarity into their endpoints and show what is actually happening on a granular level.
EDR monitors for signs of suspicious behavior and advanced threats in real time and enables users and security teams to respond to cyber threats as they happen.
But sometimes, EDR solutions can be too complex and high-maintenance for the average business to manage on its own—especially if they don’t have the right level of staff or internal resources. That’s why you’ll often find two approaches to EDR today: managed or unmanaged.
Let’s walk through the key differences between managed EDR and unmanaged EDR.
Unmanaged EDR
Unmanaged EDR can also be thought of as self-managed EDR. These solutions are typically purchased and implemented by the organization itself, which means they’re responsible for the setup, configuration, and management of the solution. It also means that unmanaged EDR solutions need someone (or likely a team of in-house staff) to actively manage, investigate, and respond to the alerts detected by the EDR.
If you are considering the unmanaged approach, the key is first to look internally and understand the goals you want to achieve through EDR—not to mention taking a hard look at your in-house team and resources.
An excellent place to start is to ask yourself what your organization can do. What, if any, endpoint products do you currently have in place? Are these products successful in reducing threats?
From there, consider these questions:
- Do you currently have enough visibility into endpoint activity?
- How effective are your current tools? Are any threats slipping through the cracks?
- How much time or expertise are you willing to commit to managing and maintaining an EDR solution? Does your team have the capacity for that?
It’s important to note that unmanaged EDR solutions are notorious for the volume of alerts they produce, and without the right team and time commitment, they may start working against you.
Managed EDR
Then, on the other hand, there is managed EDR. Managed EDR is a solution that is either offered by the EDR vendor itself or through a managed service provider (MSP). Additionally, managed EDR solutions often provide a team of experts who can help with day-to-day management, threat investigations, and alerts.
Managed EDR works in the same way an unmanaged EDR would—just without the need to set up, configure, or maintain the solution in-house.
The biggest difference with a managed EDR solution is the human-powered resources you gain. These solutions are often backed by trained professionals who can investigate potential threats and interpret the data and alerts the EDR technology produces. For the average business, that means you have a wealth of knowledge to tap into; you get an added layer of context and manual analysis that automated tools just can’t match, plus you can get the hands-on support you need when actually responding to and eliminating threats.
If the managed EDR route sounds like a good fit for your business, here are a couple of questions to keep in mind when searching for managed EDR services:
- What type of training do the security experts have?
- Have they worked with organizations like yours, and do they understand your business and the threats targeting you?
- What’s their process for monitoring endpoints and investigating potential threat activity?
- How do they ensure they pass along or act on valid threats, not false positives?
Managed EDR vs. Unmanaged EDR
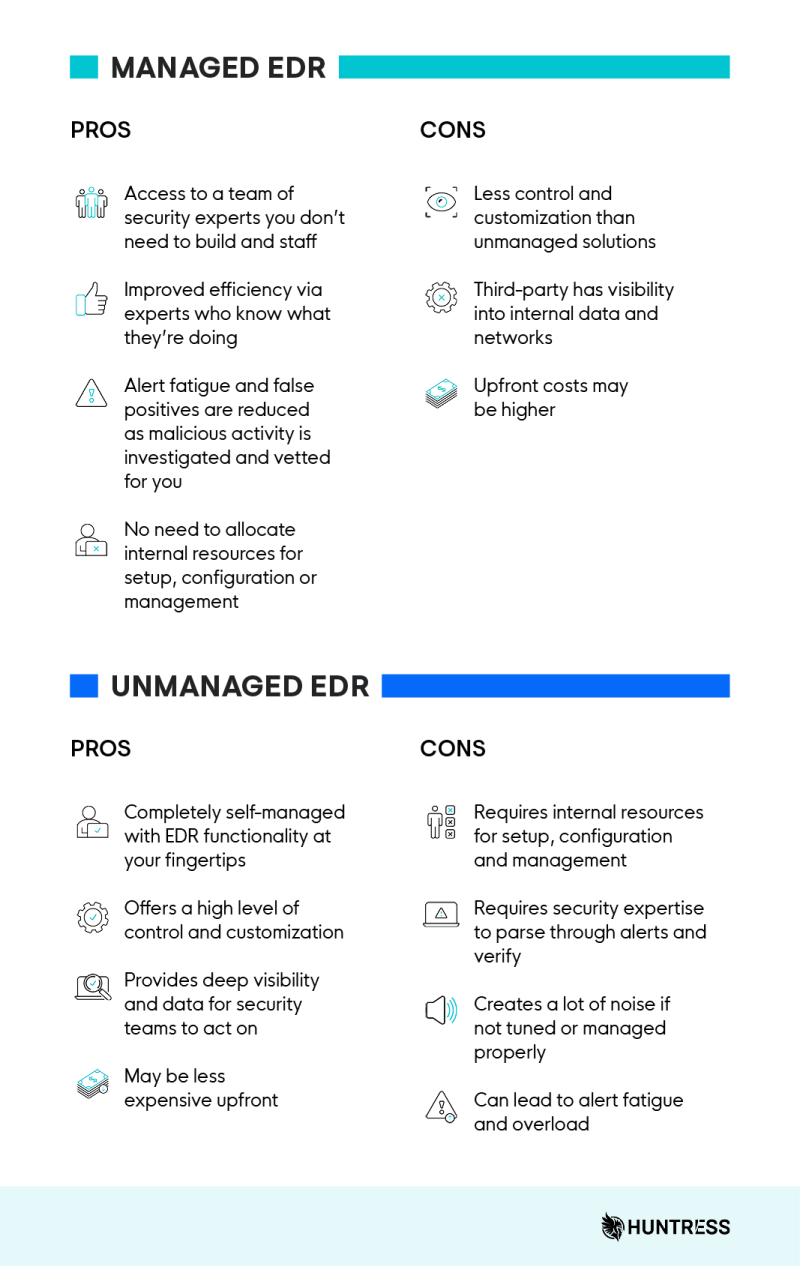
To manage or not to manage? That is the question… and each approach has its own set of pros and cons.
What EDR Solution is Best?
The answer here lies within your own organization’s capabilities and goals.
If you have a dedicated team whose sole focus is to investigate and seek out threats, an unmanaged EDR solution could fit nicely in your current security stack.
Alternatively, if you don’t have a dedicated internal security team and you lack the expertise and time to sort through alerts, then a managed EDR solution will be better suited for you. Aside from saving you from some massive headaches, managed EDR saves time and resources, reduces alerts and false positives, and helps improve your organization's overall security posture.
As always, Huntress is here to help and can be your guiding light for protection against evolving threats and determined cybercriminals.
If you’d like to see what managed EDR can do for your business, schedule a demo, and we’ll show you the power of Huntress Managed EDR.