







Hackers love to target endpoints. They are, after all, the gateway to your organization's digital infrastructure.
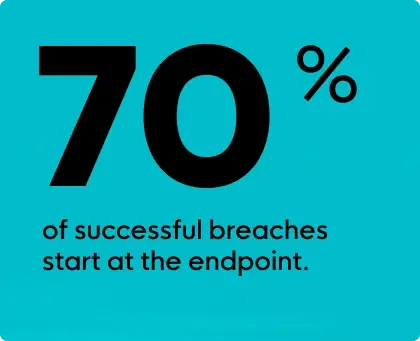
According to IDC, a staggering 70% of breaches originate at the endpoint. IT teams must now protect more endpoints—and a wider variety of endpoints—than ever before, and the perimeter has become much harder to defend. So where do you even start?
To help you navigate this space, here are nine key strategies to strengthen your endpoint security and minimize your risks.
Endpoints include everything from desktops and laptops to mobile devices and servers. Knowing the endpoints in your network is crucial for crafting a solid security strategy.
A few tips for success here:
So make that list, check it twice, and use it to tailor your defensive strategy.
Regularly updating operating systems and applications is key to endpoint security and overall good cyber hygiene. Look to create a proactive patch management strategy to address vulnerabilities promptly. To keep risk levels low, prioritize patches based on severity, and test updates in a controlled environment before rolling them out to avoid disruptions.
MFA is a great way to enhance endpoint security. By requiring users to provide multiple forms of verification—like passwords, security tokens, or biometrics—MFA significantly reduces the risk of unauthorized access. Think of it as an extra layer of protection for your endpoints. As a best practice, you should encourage the use of MFA across all devices. Be sure to review settings regularly to keep it effective.
Users and employees are your first line of defense. Regular security awareness training programs provide consistent education to help them learn how to recognize and report potential security threats. By turning users into active participants in your security efforts, you can strengthen the human element of your defense at the endpoint level and beyond.
BYOD, or “bring your own device,” allows employees to use their own computers, smartphones, or other devices for work purposes. That means there are more endpoints to defend and more entry points to fend off attackers. A well-defined BYOD policy enforces guidelines for personal device use and ensures those devices are monitored and comply with security standards.
The principle of least privilege can help you strike the right balance between security and functionality. This concept works by giving users, programs, or processes only the access they need to do their jobs. This minimizes unauthorized access while maintaining productivity.
To enforce this principle effectively, you can:
Real-time monitoring and telemetry give you a clear view of endpoint activities and behaviors, which is so critical to your endpoint security.
Look for security solutions that have real-time monitoring capabilities—this can help you detect and respond to threats quickly. And you can take things one step further by setting up alerts for suspicious activities or regularly analyzing telemetry data to spot and address emerging threats.
Think of risk assessments and audits as your cybersecurity health check-ups. Regular assessments identify potential weaknesses and areas for improvement, while audits ensure compliance with security policies. This continuous improvement cycle allows you to adapt strategies based on your findings, keeping your endpoint security solid and effective.

Endpoint detection and response (EDR) solutions are essential for a strong security strategy. EDR continuously monitors for suspicious activity at the endpoint level, allowing you to quickly detect and respond to threats. That’s really what sets EDR apart from other preventive solutions—like antivirus or firewalls—and why it’s a complementary layer in any security stack.
When looking for an EDR solution, here are a few helpful things to keep in mind:
These strategies can help strengthen your organization's defenses, and they’re a great place to start when building your endpoint security plan. But remember, endpoint security is an ongoing process that requires being vigilant and adaptable to stay ahead of today’s threats.
Get insider access to Huntress tradecraft, killer events, and the freshest blog updates.
