This blog was updated on April 17 to include threat activity we’re observing with Nightmare-Eclipse's BlueHammer, RedSun, and UnDefend exploitation techniques.
One of the many security tasks you’ve been meaning to get to: the VPN configuration sitting quietly in the backlog. You’ve been waiting for a quieter week that never comes. But attackers are counting on it staying there.
Cybercrime is a real, thriving industry, and your "hidden competition." It targets your money and resources just as any legitimate competitor would. The global cybercrime economy is estimated to surpass $10 trillion in 2025, larger than the GDP of most nations. It runs on R&D, infrastructure, automation, affiliate programs, and even forced labor, a topic we explored in depth earlier this year. All of this at a pace that rivals the Fortune 500. And one of this illicit economy’s most reliable strategies is exploiting the security obligations you haven't yet gotten around to.
Like securing your VPN.
If that sounds like a low-stakes oversight, the stories from our Security Operations Center (SOC) might give you a different perspective. All intrusions start somewhere, and all too often, it’s a simple VPN login that lacks additional security configurations.
The skeletons attackers love
Every organization has a security backlog. Tasks that linger in the background while operations move forward and the business scales. The average security team in those organizations is probably small and doing its best to prioritize. According to the Huntress How to Build a Resilient Security Team for 2030 field guide, the common sizes for IT and security teams range from six to 10 people (21.4%) and 11-15 people (19%). In some cases (18%), a single person on a team handles cybersecurity for the entire organization.
Attackers actively hunt for these gaps, because an oversight—regardless of intention—left unresolved long enough is an open invitation. Your VPN is among the most common oversights we see exploited.
Your VPN is the unlocked front door
Attackers have options. They can force their way in, but these days, most prefer to simply log in as you. Exploits and zero days are still around, but they're noisy, which kills the stealth factor. Legitimate logins are quieter and far more effective, according to analysis in the Huntress 2026 Cyber Threat Report.
Dray Agha, Senior Manager of Tactical Response at Huntress, puts it plainly in the "Breaking the Kill Chain: How to Stop Ransomware Before the Encryption Starts" webinar:
"Roughly 70% of active intrusions we catch with our SOC begin with adversaries authenticating through VPN access."
The data backs this up. Anton Ovrutsky, Manager of Tactical Response at Huntress, says:
“We see too much VPN compromise, more than we'd like to see. And in many cases, we don’t have evidence to support that the threat actor landed on the appliance via some kind of zero day.”
Multi-factor authentication (MFA) is widely recognized as a critical defense barrier to slow down attackers, but its implementation can be messy in practice, especially for the 99%. The businesses we protect may not have access to an enterprise budget: medical offices, law firms, local construction companies, veterinarians, etc. Legacy systems complicate rollouts, service accounts break, workflows change, and projects stall. MFA becomes another item on the backlog. And everything is fine, until it isn't.
Real-world insights from our SOC
When off-the-shelf tools become weapons
The VPN is often where the intrusion story starts, but what happens next can get creative.
In a recent incident, our SOC analysts noticed something unusual. There were binaries staged in places they had no business being: a low-privilege user's Pictures folder, and a two-letter subfolder buried in their Downloads directory. The filenames were a tell: FunnyApp.exe, RedSun.exe, z.exe. Not exactly the naming convention legitimate software follows.
They were looking at BlueHammer, RedSun, and UnDefend, three publicly available exploitation tools on GitHub, attributed to Nightmare-Eclipse.
Before tool execution, analysts observed a familiar sequence of hands-on-keyboard enumeration commands: whoami /priv, cmdkey /list, net group. This signaled that someone was inside the environment, figuring out what they had to work with. As for how they got in the door initially? A compromised FortiGate VPN.
Windows Defender detected and blocked BlueHammer first, which was followed by sketchy RedSun activity a few days later. But the attacker wasn't counting on Defender alone to fail. They were counting on getting enough time to escalate before anyone noticed. Alerts alone wouldn't have told the full story here. It took our SOC analysts connecting the dots to shut it down before it caused major damage.
A close call with ransomware
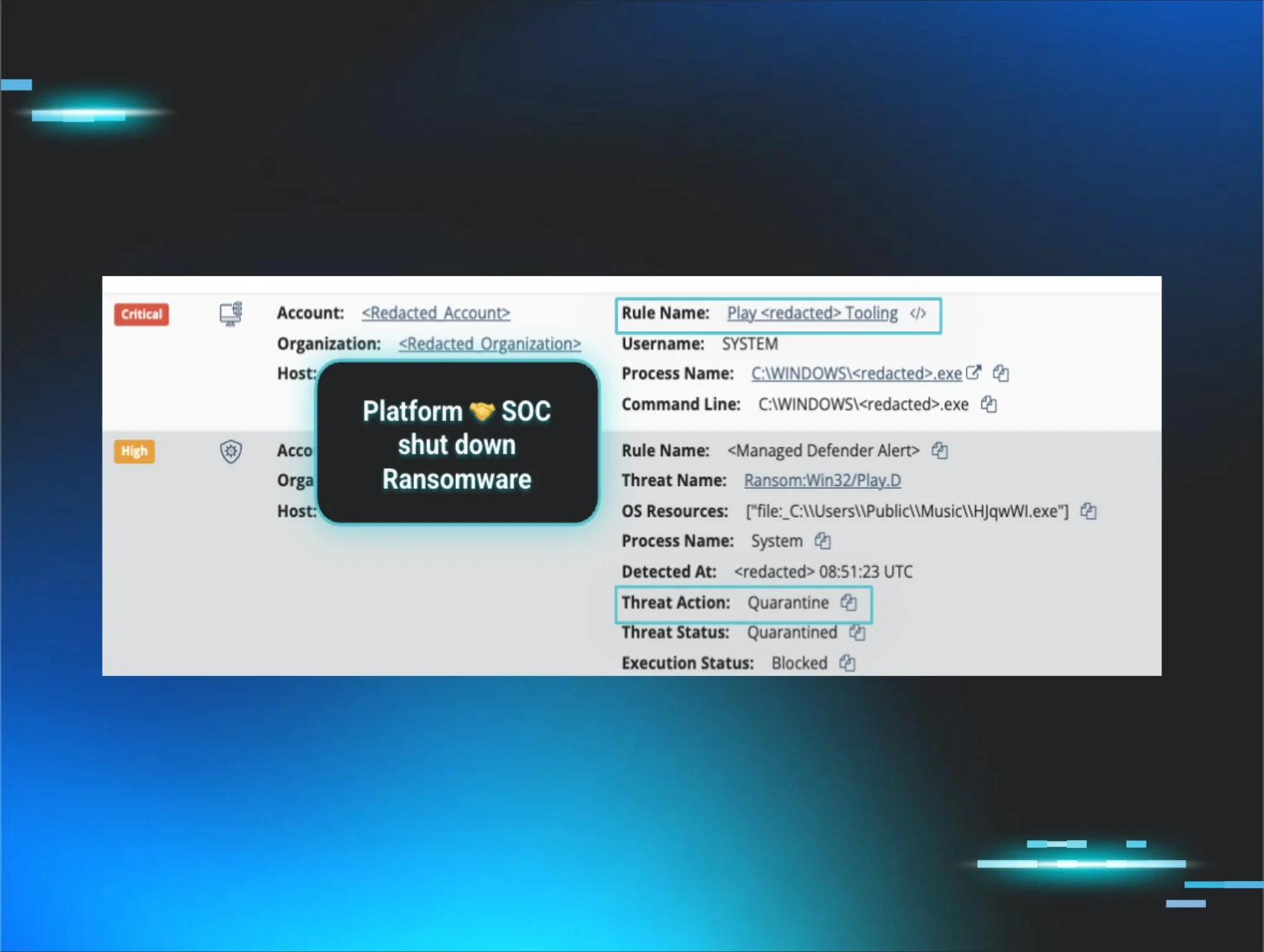
In one recent incident, an attacker authenticated to a VPN without triggering any alarms, spent time mapping the environment, pivoted to key servers, and attempted to deploy Play ransomware.
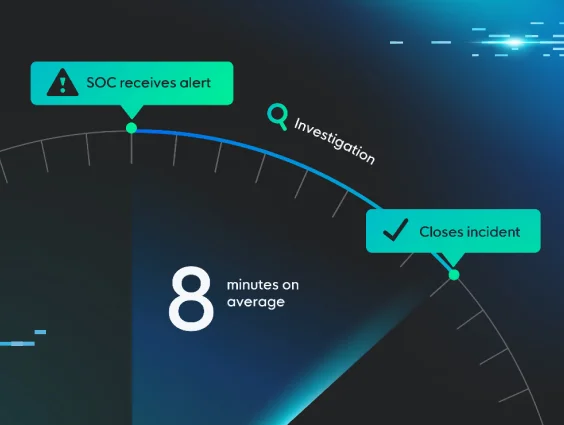
What stopped it was timing. Managed Endpoint Detection and Response (EDR) and Managed Microsoft Defender fired off fast warning signals, and our SOC analysts jumped in before encryption had a chance.
Without this resilience plan, this business would've faced operational downtime, pricey recovery, reputational damage, and days of disruption. Instead, they got a hard lesson in cleaning up their VPN attack surface.
Figure 1: Shutting down a ransomware attempt stemming from unauthorized VPN authentication
When VPN logs disappear
Here's a pattern we see too often: missing logs.
In many instances, the first evidence of a VPN intrusion vanishes due to data storage issues before any investigation can begin. When we respond to incidents without centralized logging, we're often piecing together a story that starts halfway through.
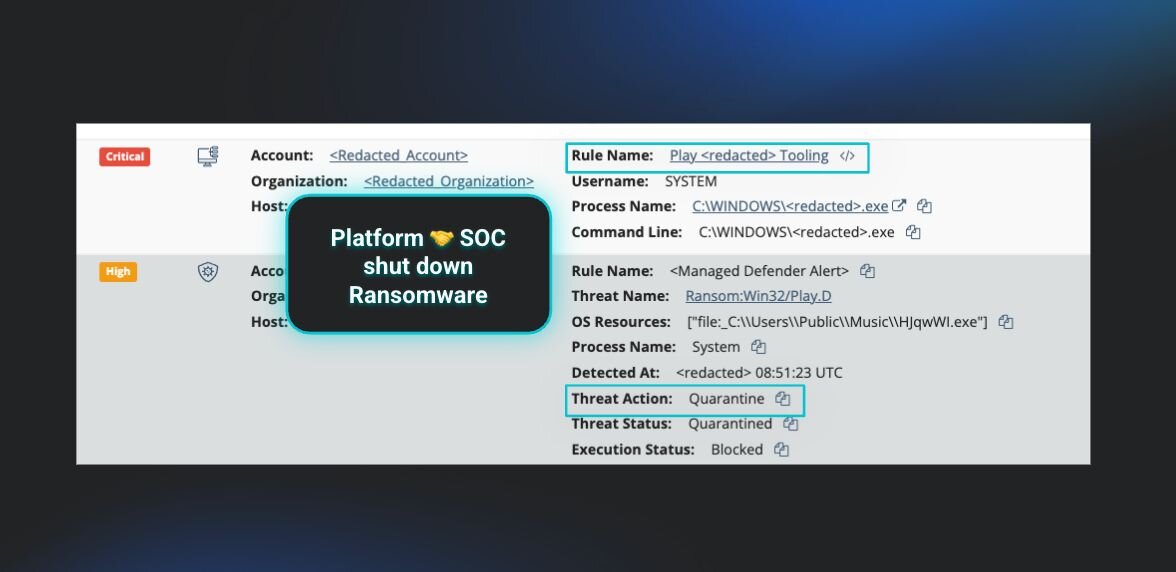
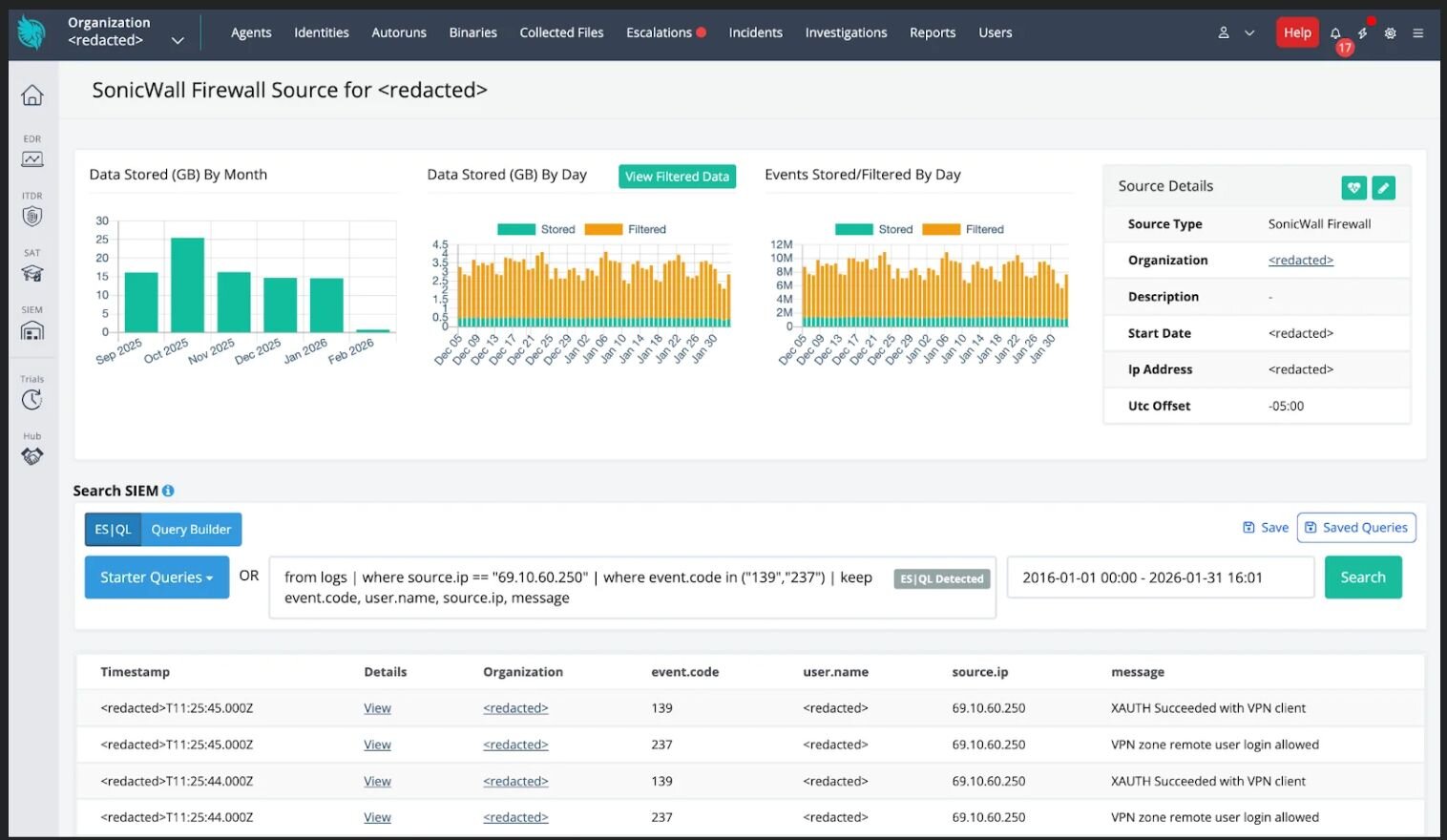
This is where a Security Information and Event Management (SIEM) solution is essential. It preserves the full timeline of an intrusion, starting with the opening act, so defenders can understand not just what happened, but what needs to be fixed to prevent it from happening again.
Missing VPN logs aren't just missing information. They're blind spots that attackers will keep exploiting.
Red carpet access
In another case, a threat actor compromised SonicWall SSLVPN credentials and landed inside the target environment with administrative privileges that were handed to them on a silver platter by two compounding gaps: no MFA and no network or account segmentation.
Once inside, the attacker conducted network discovery via ping sweeps, then deployed Bring Your Own Vulnerable Driver (BYOVD) tactics to enumerate security tools, disable defenses, and establish persistence. Our SOC analysts caught and contained it, but the initial access was an easy win for the attacker.
Figure 2: Huntress Managed SIEM dashboard showing VPN successful authentication events from the threat actor’s IP
One thing to check off your list this week
These incidents share a common thread: attackers didn't need to work hard. And fixing that doesn't mean you have to tackle everything at once.
If your VPN security has gaps, start here: enforce MFA. It's the single highest-impact step you can take, and it's the one that would've made both of the stories above significantly harder for the attacker.
After that, work the list in order of effort:
Audit privileged accounts. Remove admin rights that aren't actively needed. The SonicWall case handed an attacker admin access they had no business having.
Disable legacy and unused accounts. Old credentials are easy targets and readily available on dark web marketplaces.
Centralize your logs. You can't investigate what you can't see, and you can't fix what you can't trace back to the source.
Monitor for login anomalies, enforce allow/deny lists, and use strong, unique passwords. Lower lift, but worth locking in once the bigger items are done.
This isn't about a perfect backlog. It's about making your environment intentionally tougher to exploit than last week.
We talk about VPN security a lot. You might wonder why we keep coming back to it.
Because resilient teams understand that some things will get missed. So they plan for that reality. They prioritize speed over volume, treat identity as a major attack surface, and build clear ownership to limit damage and recover quickly. For lean teams covering an entire organization, perfection usually isn’t realistic. What matters is having the visibility and response capability to catch what slips through before it turns into something worse.
Want to learn more about the cybercrime ecosystem? Check out our _declassified webinar series.